Learn
Guides and explainers on crypto wallet security, exchange risks, and setup best practices. No hype.
Social Engineering in Crypto: Why People Are Now the Main Target
Social engineering now causes more than 60% of crypto losses. See how attackers build trust, the tactics they use, and how to protect your setup.
DeFi Bridge Security Risks: What Holders Need to Know
Cross-chain bridges are among the most exploited targets in DeFi. Here's how they fail, what the 2026 hacks show, and how to limit your exposure.
Pig Butchering: The Crypto Scam Built on Fake Relationships
Pig butchering scams cost Americans $8.6 billion in 2025. Learn how this long-con crypto investment fraud works and how to spot one before it starts.
SIM Swap Attacks: How Hackers Hijack Crypto Accounts via SMS
SIM swap attacks give hackers control of your phone number, bypassing SMS 2FA on crypto accounts. Here is how they work and how to stop them.

Private Key Compromise: The Attack Behind Most Crypto Losses
Most crypto theft in 2025 came from private key compromise, not code exploits. Here is how keys are stolen and what it means for your setup.

Crypto Wrench Attacks: Physical Security for Crypto Holders
Physical crypto theft via wrench attacks rose 75% in 2025. Learn how attackers identify targets and what setup changes reduce your exposure.

Address Poisoning in Crypto: How Fake Addresses Steal Millions
Address poisoning attacks plant fake lookalike wallet addresses in your transaction history. One wrong copy-paste can send your assets to an attacker.

DeFi Token Approvals: How Unrevoked Permissions Drain Wallets
Every DeFi interaction creates an on-chain permission that stays active until revoked. How token approvals work and how to check your exposure.

Fake Crypto Apps in Official App Stores: How to Spot Them
Fake crypto apps have appeared in the Apple App Store and Google Play. Here is how they bypass review, what they do once installed, and what to check.

What Is an MPC Wallet and When Should You Use One
MPC wallets split your private key into shares across multiple parties, removing any single point of failure. Learn when MPC makes sense for your setup.

Hot Wallet vs Cold Wallet: How to Decide What Goes Where
How to split your crypto holdings between hot and cold storage, and what should determine where each asset lives in your setup.

How to Check If Your Hardware Wallet Has Been Tampered With
Check a hardware wallet for tampering before use: physical signs, Ledger and Trezor verification tools, and the most common supply chain risks.

North Korean Crypto Theft: Scale, Tactics, and Your Exposure
North Korean hackers stole $2.02 billion in 2025, nearly 60% of all crypto stolen globally. Learn how Lazarus Group operates and what it means for your setup.

How Crypto Attackers Now Target Individual Holders
In 2025, individual holders became the top target for crypto attackers. Social engineering and whale hunting now drive more losses than protocol exploits.

AI Crypto Scams: How Deepfakes and Voice Cloning Are Used
AI-powered scams stole $17 billion in 2025, with impersonation fraud up 1,400%. Here is how deepfakes and voice cloning work and what to check in your own setup.

Multi-Signature Wallets: When They Make Sense for Crypto Holders
Multisig wallets require more than one key to authorize a transaction, removing single points of failure in self-custody setups. Learn when they make sense.

How to Store Your Seed Phrase Without Losing Access
Your seed phrase is the only key to your wallet. This guide covers the right materials and locations for a backup that lasts and stays secure.
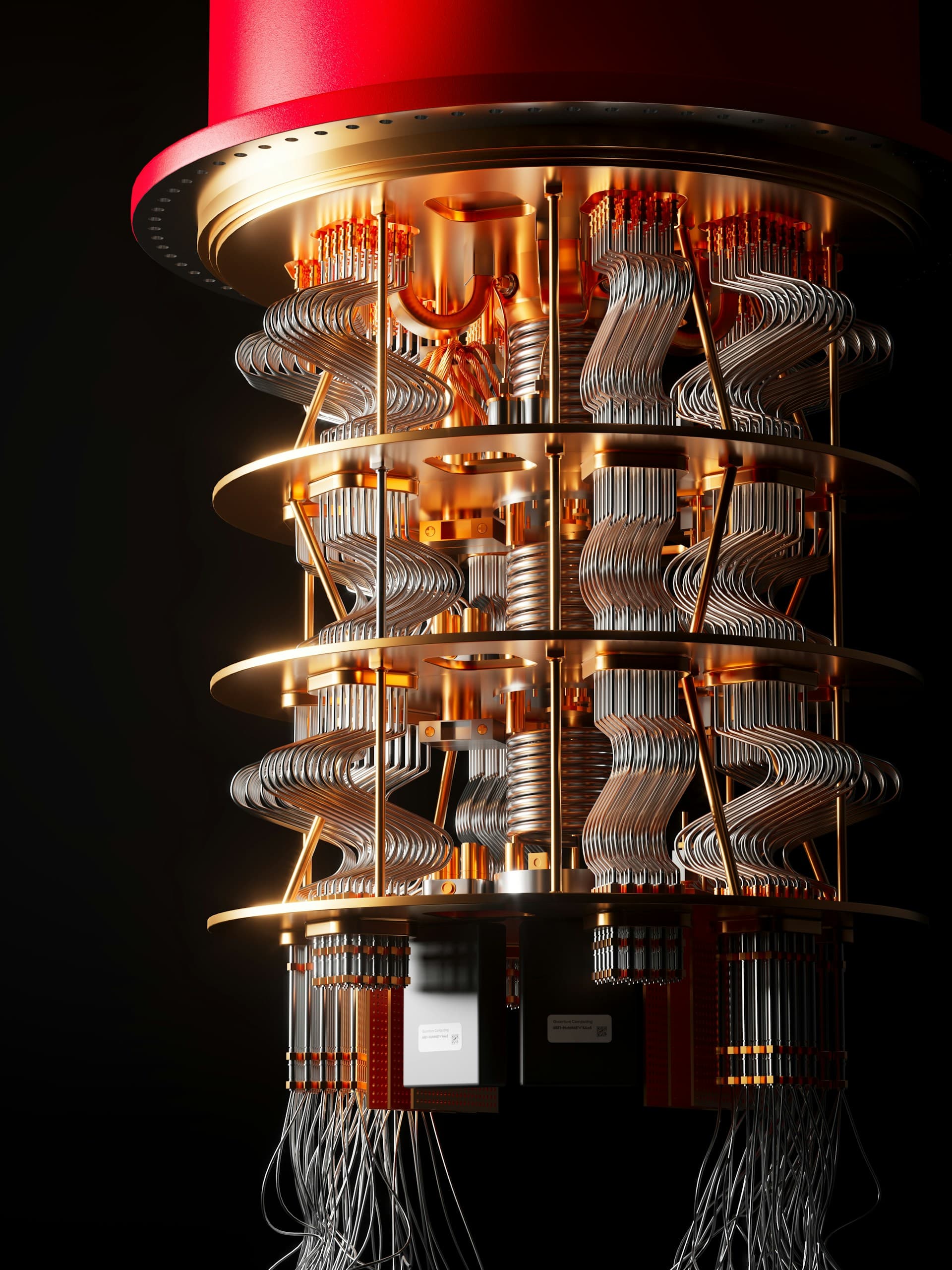
Quantum Computing and Crypto: What Holders Need to Know
How quantum computing threatens Bitcoin and Ethereum security, which addresses are at risk today, and what major networks are doing about it.

Hardware Wallet Blind Signing: The Risk Behind the Button
Blind signing lets attackers drain your assets with a single approval — no seed phrase required. Here's what it means and what to check in your setup.

The Bybit Hack: What It Means for Your Exchange Holdings
In February 2025, hackers stole $1.5 billion from Bybit without touching the exchange directly. Here's what that means for anyone holding assets on exchanges.

Crypto Phishing Scams: How They Work and How to Avoid Them
Crypto phishing scams cost holders $17 billion in 2025. Learn how impersonation attacks, wallet drainers, and address poisoning work — and what to do.

Why 2FA Alone Isn't Enough to Protect Your Crypto
Two-factor authentication is a good start, but it's just one layer. Learn what else you need to truly secure your crypto holdings.

The Danger of Single-Platform Dependency
Keeping all your crypto on one platform is like keeping all your savings in one bank — except without FDIC insurance.

Three Proven Wallet Configurations for Different Portfolio Sizes
Whether you hold $500 or $500,000 in crypto, there's an optimal setup. Here are three battle-tested configurations.