Hardware Wallet Blind Signing: The Risk Behind the Button

Why this matters
If you use a hardware wallet with DeFi, you've likely approved transactions your device couldn't fully display. A single blind-signed approval can grant a contract unlimited access to your tokens — no seed phrase needed. Checking your wallet's clear-signing support and reviewing open approvals are two steps you can take today to close this gap.
Hardware wallet blind signing is the practice of approving a transaction where your device displays only a raw hash — not the underlying action. As DeFi interactions become routine, the approval button has become a primary target for drainer attacks that do not require your seed phrase at all.
What your hardware wallet actually shows you
When you interact with a smart contract — swapping tokens on a DEX, minting an NFT, or bridging assets — your wallet receives a bundle of encoded data. If the wallet app cannot decode that data into plain language, the device shows "Data Present" or a hex string and asks you to confirm. That is blind signing.
The problem is not the hash itself. The problem is what it can contain. A single signed approval can grant a smart contract unlimited access to every token in your wallet. It can authorise an NFT sweep. It can, via mechanisms like EIP-712, delegate control to an address you never see. You press the button, the device does exactly what it was told — you just did not know what you were telling it to do.
Clear signing, by contrast, means your device decodes the transaction into legible fields before displaying it: recipient address, token type, amount, contract function name. You confirm what you can read. Wallets that support clear signing for a given contract are substantially harder to exploit through approval manipulation.
How attackers use a single approval to empty wallets
Approval-based phishing relies entirely on blind signing. An attacker creates a malicious dApp — or compromises a legitimate one — and presents a transaction that looks routine but contains a hidden setApprovalForAll or permit instruction. The user, seeing only "Data Present," confirms. The attacker then calls the contract to sweep the assets at a time of their choosing.
The $1.5 billion Bybit hack in February 2025 — the largest crypto theft on record — followed this pattern at scale. The Lazarus Group manipulated the signing interface used by Bybit's authorised signers so that what appeared to be a routine internal transfer was actually a transfer of control to an attacker-controlled contract. Seed phrases never moved. The signing process was the vulnerability.
Drainer-as-a-service kits have industrialised this approach. Operators subscribe to a kit, clone a convincing dApp front end, and distribute phishing links. Crypto phishing losses totalled $84 million across 106,000 victims in 2025, down 83% from the prior year — but analysts note the drainer ecosystem remains active, with new kits replacing those that shut down (Scam Sniffer, 2025). A newer attack surface opened when Ethereum's Pectra upgrade shipped EIP-7702, which allows multiple actions to be bundled into a single signature; two major cases exploiting this mechanism resulted in $2.54 million in losses shortly after launch (Scam Sniffer, 2025).
What to check in your own setup
The clearest mitigation is to separate your high-value storage from your active DeFi address. Keep the wallet holding significant assets in cold storage, and use a separate address — funded only with what you need for a specific session — when interacting with contracts you have not used before. An attacker who tricks your active wallet into a bad approval can only reach what is in that wallet.
Beyond segregation, review your current approvals. Tools like Revoke.cash let you see every contract holding an active approval against your address. Revoke anything you no longer use, especially unlimited approvals.
When evaluating a hardware wallet, check for clear signing support on the chains and contract types you actually use. Some wallets support clear signing natively for ERC-20 transfers but require a companion plug-in for NFT or DeFi contracts — the coverage varies by device and chain. If your device cannot decode a transaction, treat the request as untrusted until you can verify it elsewhere.
To see how your current setup scores across this and related gaps, check your setup in the Asset Alert app.
Frequently asked questions
See your health score in under five minutes.
No wallet connection. No account needed to start. Just map your setup and get a clear picture of where the gaps are.
Related Articles
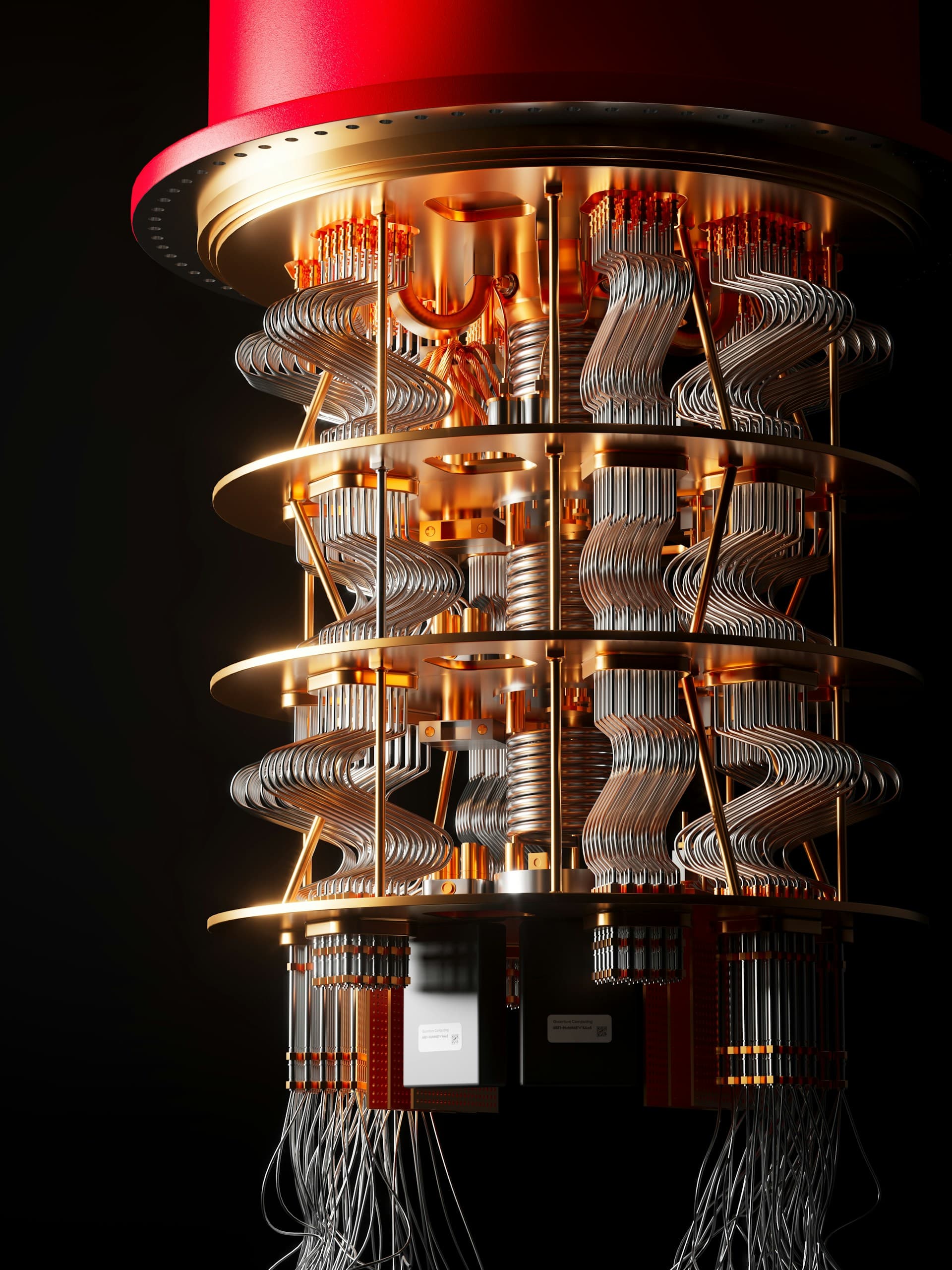
Quantum Computing and Crypto: What Holders Need to Know
How quantum computing threatens Bitcoin and Ethereum security, which addresses are at risk today, and what major networks are doing about it.

Crypto Phishing Scams: How They Work and How to Avoid Them
Crypto phishing scams cost holders $17 billion in 2025. Learn how impersonation attacks, wallet drainers, and address poisoning work — and what to do.

Why 2FA Alone Isn't Enough to Protect Your Crypto
Two-factor authentication is a good start, but it's just one layer. Learn what else you need to truly secure your crypto holdings.