Quantum Computing and Crypto: What Holders Need to Know
Why this matters
Quantum computers don't threaten your crypto today, but the timeline for when they might has shortened significantly. If you hold Bitcoin or Ethereum long-term, the type of address you use and whether your public key is exposed on-chain affects your future risk. Understanding the basics now helps you pick the right wallets and address formats before it becomes urgent.
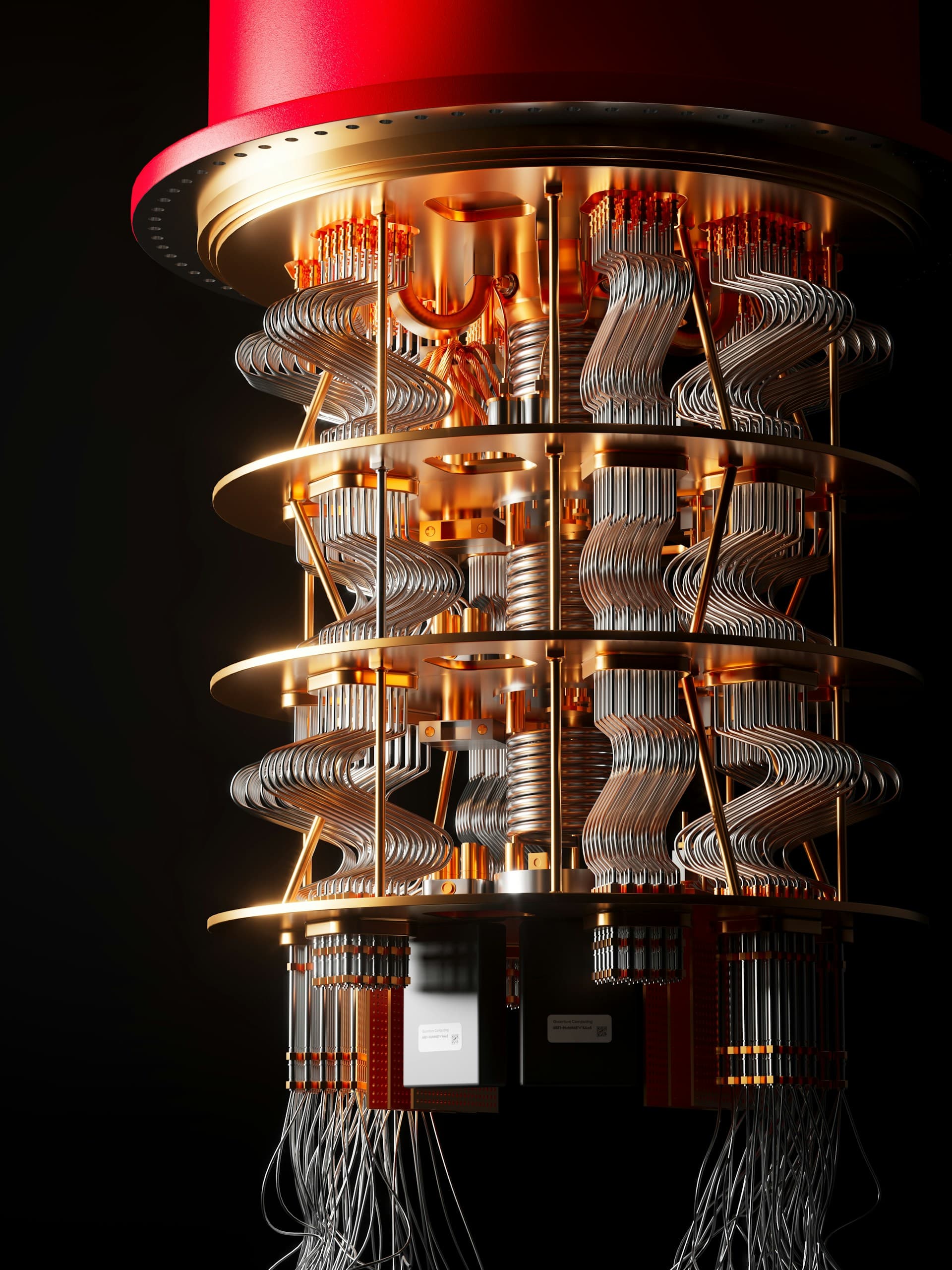
Quantum computing is moving from theoretical threat to active engineering concern for the crypto industry. Three research papers published between January and March 2026 significantly reduced the estimated computing power needed to break the elliptic-curve cryptography that secures Bitcoin, Ethereum, and most major blockchains. This article covers what the updated timeline means for holders, which addresses are most exposed, and what the major networks are doing to prepare.
Why the Threat Timeline Moved
Until recently, breaking ECDSA — the signature scheme protecting wallet transactions — was estimated to require tens of millions of physical qubits. Research published in early 2026 reduced that figure sharply: Google's Quantum AI team estimated that fewer than 500,000 physical qubits could break elliptic-curve cryptography (The Quantum Insider, 2026), and a separate study reported that as few as 10,000 to 26,000 qubits could break ECC-256 in approximately ten days (CoinDesk, March 2026).
No quantum computer of that scale exists today. Google's most advanced systems operate at around 100 qubits; fault-tolerant machines capable of cryptographic attacks remain years away. The Global Risk Institute's 2026 Quantum Threat Timeline puts a cryptographically relevant quantum computer as possible within 10 years and likely within 15. Q-Day is not imminent.
What shifted is the accuracy of estimates, and with it the urgency of preparation. Networks that need years of lead time to deploy protocol changes are right to begin now, not when the hardware catches up.
Which Crypto Addresses Are Most Exposed
Not all holdings carry the same quantum exposure. The risk depends on whether a wallet's public key is visible on-chain.
Bitcoin uses a two-step hash to derive addresses from public keys. If an address has never sent a transaction, only the hash is public — not the key itself. Addresses that have received funds but never spent them are substantially harder to attack. By contrast, every address that has broadcast a transaction exposes its public key directly in the signature. A 2025 Chaincode Labs study estimated that roughly 20–50% of circulating Bitcoin addresses are in this exposed state, representing approximately 6.26 million BTC (Chaincode Labs, 2025).
Ethereum is inherently more exposed because every account's public key is permanently visible on-chain, regardless of transaction history. There is no hash-only protection layer. The Ethereum Foundation published a quantum preparedness roadmap in February 2026 and established a dedicated research team in 2025 to address this gap.
For hardware wallet holders, the private key stays offline — quantum computing does not change that. The exposure is at the on-chain signature layer, not at key storage.
What to Check in Your Own Setup
Bitcoin, Ethereum, and Solana are taking different approaches to post-quantum readiness. Ethereum has committed to a phased migration toward NIST-standardized post-quantum signature schemes — ML-DSA and ML-KEM, finalized in August 2024 (NIST, 2024). Algorand completed its first mainnet Falcon-1024 transaction in November 2025 (CoinDesk, 2025). Bitcoin's path is less settled; a prototype migration tool for potentially exposed addresses was released by Lightning Labs in April 2026, but no protocol-level upgrade is confirmed.
For most holders, no immediate action is required. A few practices reduce long-term exposure:
- Avoid address reuse. Sending from an address reveals its public key on-chain; using fresh receive addresses limits future exposure.
- Use hardware wallets for long-term holdings. Private keys stay offline and are not affected by quantum key-breaking scenarios.
- Monitor protocol announcements. When major networks activate quantum-resistance upgrades, migration windows will open. Knowing your setup in advance makes the transition straightforward.
You can map your current setup and see which platforms hold your assets at Asset Alert.
Frequently asked questions
See your health score in under five minutes.
No wallet connection. No account needed to start. Just map your setup and get a clear picture of where the gaps are.
Related Articles

Hardware Wallet Blind Signing: The Risk Behind the Button
Blind signing lets attackers drain your assets with a single approval — no seed phrase required. Here's what it means and what to check in your setup.

Crypto Phishing Scams: How They Work and How to Avoid Them
Crypto phishing scams cost holders $17 billion in 2025. Learn how impersonation attacks, wallet drainers, and address poisoning work — and what to do.

Why 2FA Alone Isn't Enough to Protect Your Crypto
Two-factor authentication is a good start, but it's just one layer. Learn what else you need to truly secure your crypto holdings.