How Crypto Attackers Now Target Individual Holders
Why this matters
The risk model has changed: attacks on individual holders through social engineering, impersonation, and physical coercion now account for the majority of crypto losses. Holders with visible wealth on-chain or on social media face higher exposure than those whose setup is less conspicuous. Reviewing what information is publicly visible and what token approvals are active is now as important as choosing where to store assets.
The threat landscape for crypto holders shifted significantly in 2025. The largest losses no longer came from protocol exploits or exchange hacks. Criminal groups replaced mass-spam phishing campaigns with targeted, high-value operations against individual holders. Overall theft totals stayed near record highs even as the number of victims fell, because each successful attack on a single person yielded far more than a broad phishing run.
Why Individual Holders Are Now the Primary Target
Historically, the most lucrative attacks hit protocols and exchanges: compromise one smart contract or hot wallet, extract millions in seconds. That model still exists, but the trend is shifting. According to Chainalysis, social engineering accounted for 55.3% of exploit-related value taken in 2025, totaling $1.39 billion. Wallet compromises alone affected 158,000 incidents across 80,000 unique victims.
The logic is clear: protocols hire security researchers and run code audits. Individual holders typically do not. A high-net-worth holder who openly discusses holdings on social media becomes a soft target for an attacker willing to invest days of reconnaissance before acting. Criminal groups now call this "whale hunting," shifting from casting a wide phishing net to running personalised operations against a small number of high-value individuals.
In November 2025, the number of phishing victims fell 42% while total losses from those attacks spiked 137% (Chainalysis, 2026). Fewer victims, much larger individual losses. The data confirms that when attackers invest more effort per target, returns are substantially higher.
How These Targeted Attacks Work
Most individual-targeted attacks combine several techniques. Social engineering is the entry point: attackers impersonate exchange support staff, trusted colleagues, or regulatory bodies. Phishing tactics have evolved from generic mass emails to personalised messages that reference real account details, recent transactions, or a holder's registered name. AI-generated voice clones make phone-based impersonation harder to detect; AI-enabled impersonation scams were reportedly 4.5 times more profitable than traditional scams in 2025 (Chainalysis, 2026).
Once contact is established, attackers push toward one of several goals:
- Seed phrase extraction: Creating a false sense of urgency, such as an imminent account closure, to get a holder to enter their recovery phrase on a controlled site
- Malicious transaction signing: A pre-built transaction that appears routine but bundles approvals or large transfers in one step, a risk closely related to the blind signing exposure that affects hardware wallet users
- Device compromise: Infected software disguised as legitimate tools, installing stealers that read clipboard data, browser-stored keys, and wallet files
Physical coercion is also rising. "Wrench attacks," where holders are physically forced to hand over devices or seed phrases, reached 72 verified cases globally in 2025, a 75% increase over the prior year (The Block, 2026).
What to Check in Your Own Setup
The most effective defenses are often operational, not technical. Remove social media posts that reveal the scale of your holdings. Avoid naming specific exchanges or hardware wallets you use in public forums, since this narrows what an adversary needs to study. Review open token approvals across your DeFi wallets: an approval granted months ago can be exploited whenever an attacker decides to act on it.
For significant holdings, consider a multisig setup that requires signing from more than one device. Any attacker who gains access to a single key cannot move assets unilaterally. If you are not yet using a hardware wallet, assets in software wallets are exposed to the device-compromise vector, where a single infected application can drain multiple wallets at once.
You can map your current setup and check for concentration, open approvals, and other gaps at Asset Alert. Seeing your setup laid out visually often surfaces issues that are easy to miss when managing assets across multiple platforms.
Frequently asked questions
See your health score in under five minutes.
No wallet connection. No account needed to start. Just map your setup and get a clear picture of where the gaps are.
Related Articles
AI Crypto Scams: How Deepfakes and Voice Cloning Are Used
AI-powered scams stole $17 billion in 2025, with impersonation fraud up 1,400%. Here is how deepfakes and voice cloning work and what to check in your own setup.
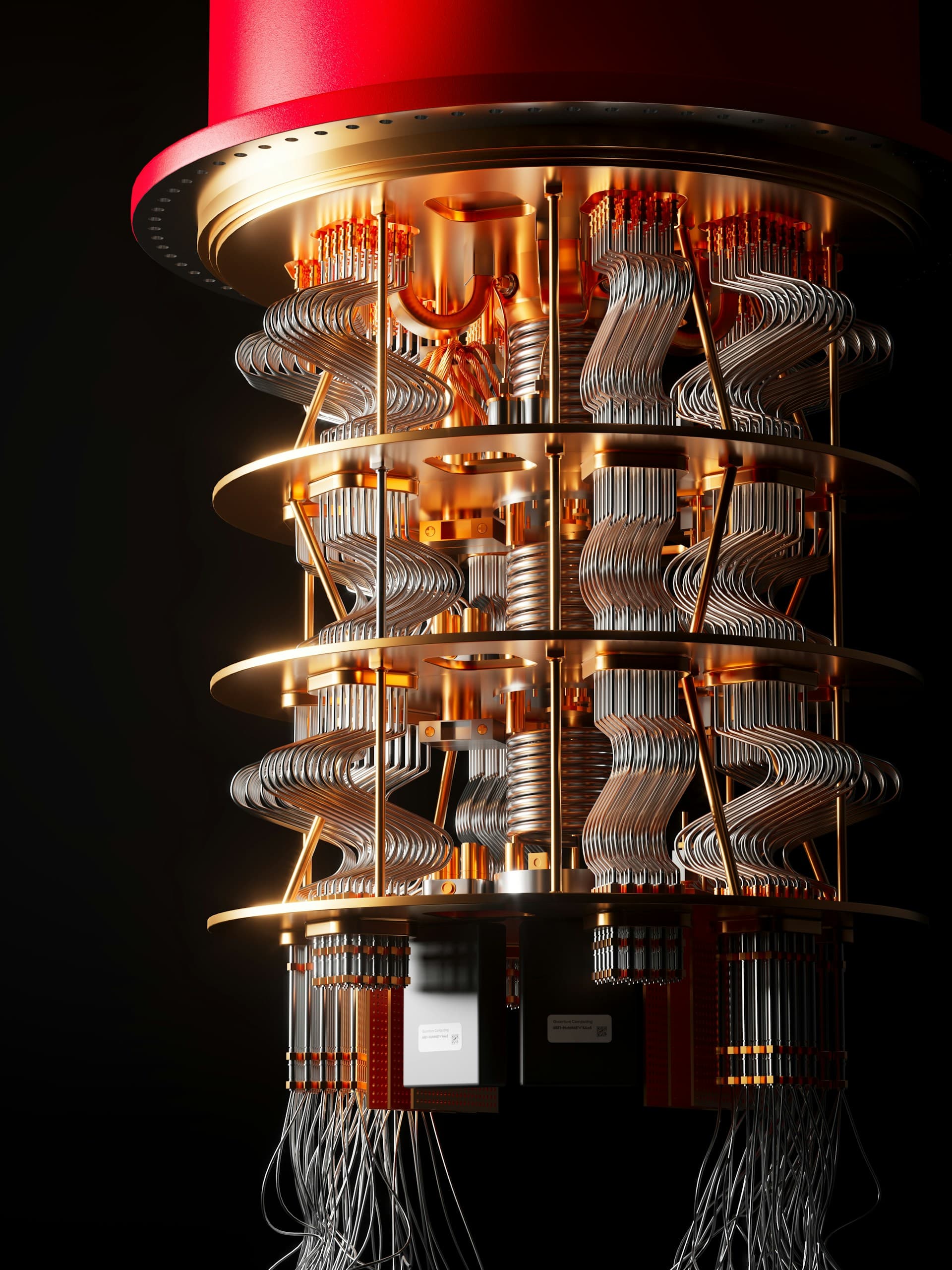
Quantum Computing and Crypto: What Holders Need to Know
How quantum computing threatens Bitcoin and Ethereum security, which addresses are at risk today, and what major networks are doing about it.

Hardware Wallet Blind Signing: The Risk Behind the Button
Blind signing lets attackers drain your assets with a single approval — no seed phrase required. Here's what it means and what to check in your setup.