North Korean Crypto Theft: Scale, Tactics, and Your Exposure
Why this matters
North Korean state-sponsored hackers stole $2.02 billion in cryptocurrency in 2025, nearly 60% of all crypto stolen globally that year. Any exchange or DeFi protocol you use is a credible target. Reducing concentration across platforms and moving long-term holdings into self-custody are the most direct steps to limit exposure.
North Korean crypto theft reached a historic scale in 2025, with state-sponsored hackers stealing $2.02 billion across dozens of incidents, a 51% increase over the prior year (Chainalysis, 2025). Those operations now account for nearly 60% of all cryptocurrency stolen globally, and the group behind them is targeting exchanges and DeFi protocols that ordinary holders use every day. Understanding how they work is the first step in knowing whether your own setup carries exposure.
How the Lazarus Group Runs Its Operations
Lazarus Group is a state-sponsored hacking unit linked to North Korea's Reconnaissance General Bureau. Their operating model has shifted significantly in recent years, away from purely technical exploits and toward social engineering and long-term infiltration.
Their entry points now include fabricated professional identities, multi-month relationship-building campaigns with employees at crypto firms, and malware delivered inside job-application or interview documents. If you recognise these patterns from crypto phishing attacks, that is not a coincidence: the tactics overlap, but DPRK operations are typically sustained over a longer period and target people with platform access rather than individual holders directly.
North Korean IT workers have also embedded themselves as legitimate contributors inside DeFi codebases over periods of years, contributing working code before enabling a coordinated breach at an opportune moment. Reports indicate this tactic affected approximately 40 DeFi projects (CoinDesk, 2026).
Their largest single operation in 2025 was the February breach of Bybit, resulting in $1.5 billion in losses, the largest single crypto theft on record (Chainalysis, 2025). As covered in the Bybit hack analysis, the attack did not defeat cryptographic systems. It compromised the multi-signature signing workflow used to authorise large withdrawals, targeting human process rather than code. After each major theft, the group follows a consistent laundering sequence over roughly 45 days: moving assets through Chinese-language money services, cross-chain bridges, and crypto mixers to obscure the trail (TRM Labs, 2025).
What This Means for Exchange and DeFi Holders
The scale of Lazarus Group activity means any centralised exchange or DeFi protocol you hold assets on is a credible target. DPRK-linked actors accounted for 76% of all service-level compromises in the crypto sector in 2025, despite the total number of North Korean incidents falling 74% year-on-year (Chainalysis, 2025). They are achieving larger results with fewer, more precisely targeted attacks.
For exchange holders, this is a custodial risk: the platform holding your assets is the target, not your individual account. Customers holding assets on Bybit at the time of the breach faced losses through no error or action of their own. Concentration on a single exchange amplifies this: if that platform is hit, the entire balance held there is exposed.
For DeFi holders, the risk is different. DPRK-linked contributors have reportedly had access to codebases at projects including SushiSwap, THORChain, and Fantom (CoinDesk, 2026). Assets staked in a protocol with embedded backdoor access can be drained through mechanisms put in place long before any public breach is detected.
What to Check in Your Own Setup
The most direct way to reduce exposure to exchange-based theft is to move long-term holdings off exchanges and into self-custody. Hardware wallets remove the custodial risk that makes exchange breaches damaging: assets held off-platform are not exposed if the exchange itself is compromised. For any exchange holdings you keep, confirm that 2FA is enabled and that withdrawal address whitelisting is active where the option is available.
For DeFi exposure, check how many open token approvals you currently have across protocols. Each approval grants a smart contract ongoing spending access to a token in your wallet. Revoking unused approvals reduces the attack surface if a protocol is found to have been compromised.
The risks of concentrating assets on a single platform apply here too: a single exchange or protocol holding the majority of your balance creates one point of failure. You can map your full setup and review it for concentration gaps at /app.
Frequently asked questions
See your health score in under five minutes.
No wallet connection. No account needed to start. Just map your setup and get a clear picture of where the gaps are.
Related Articles
How Crypto Attackers Now Target Individual Holders
In 2025, individual holders became the top target for crypto attackers. Social engineering and whale hunting now drive more losses than protocol exploits.
AI Crypto Scams: How Deepfakes and Voice Cloning Are Used
AI-powered scams stole $17 billion in 2025, with impersonation fraud up 1,400%. Here is how deepfakes and voice cloning work and what to check in your own setup.
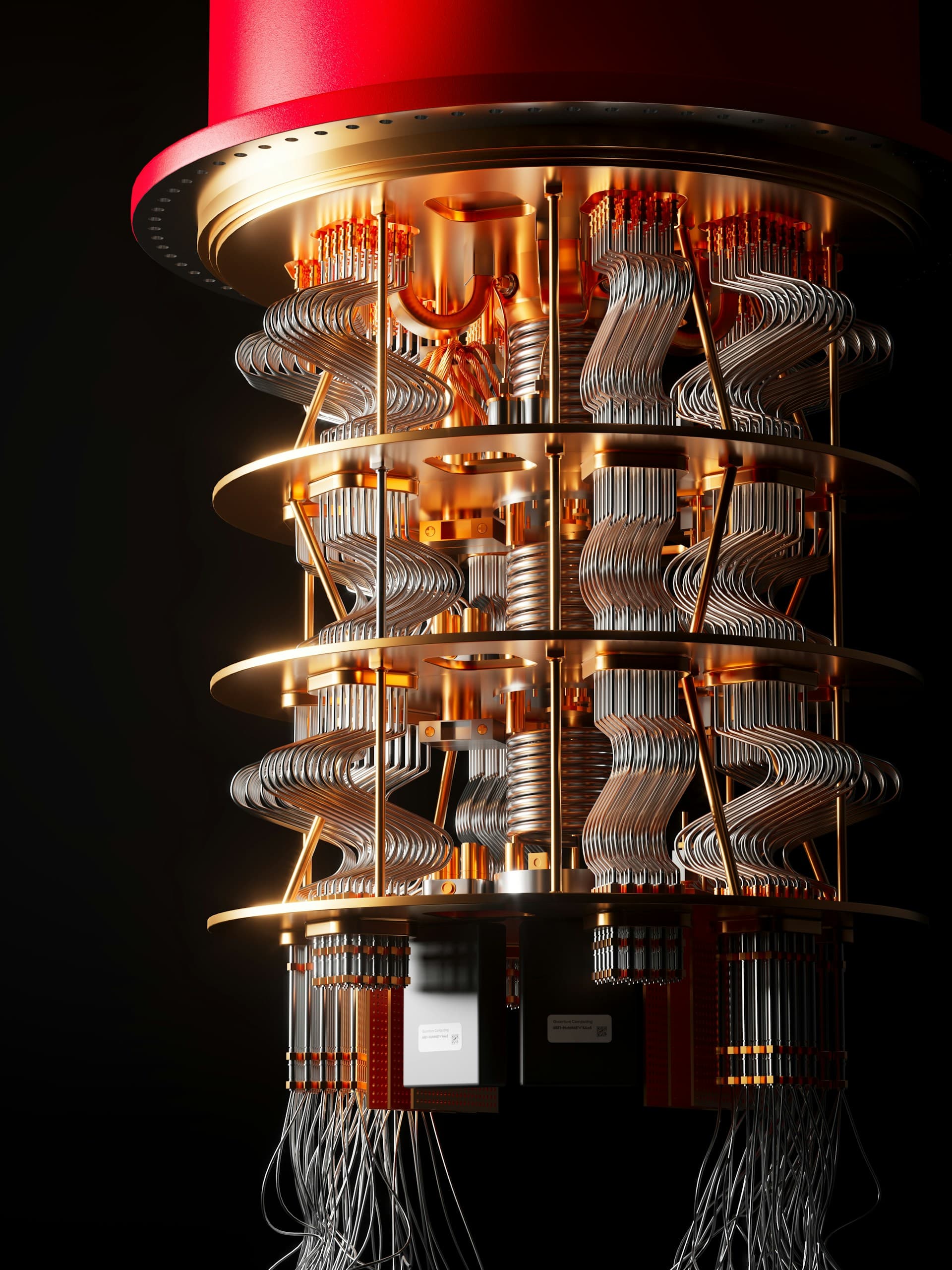
Quantum Computing and Crypto: What Holders Need to Know
How quantum computing threatens Bitcoin and Ethereum security, which addresses are at risk today, and what major networks are doing about it.